Batch 18
Post Graduate Certificate in Cybersecurity
- #1 Private University as per QS Global World Ranking 2025
- Earn a certificate from MIT xPRO and 40 CEUs
- Live masterclass on Gen AI and cybersecurity tools by industry experts
Invalid liquid data
Unlock Your Potential
Emeritus is collaborating with MIT xPRO to help you build future-ready skills. Enroll before Invalid liquid data and get 5% tuition assistance to set yourself up for professional success. Use Code UNLOCKBC05LP3398 during payment to avail tuition assistance.
Get a Headstart with a Personalized Tour. Watch this!
Watch this orientation video, as Dr. Keri Pearlson introduces your learning journey into core cybersecurity concepts, emerging technologies, and practical skills—preparing you for a high-demand, impactful career in the field.

Program Highlights
Earn a certificate from MIT xPRO to elevate your credentials
Insights and case studies from renowned MIT faculty
Market-ready cybersecurity skills in a high-growth market
Capstone presentation project to share with potential employers
Access to cutting-edge tools and frameworks from MIT faculty
Bi-weekly doubt clearing session with program leader

Live Masterclasses with program leader for hands-on learning
Program Frameworks
The NIST CSF framework is threaded throughout the entire program as a commonly used framework. It is a widely used cybersecurity framework that encompasses guidelines for organizations to prepare themselves against cybersecurity attacks.
The Cloud Security Alliance (CSA) Cloud Controls Matrix (CCM) is discussed in the defensive cybersecurity section. This framework includes domains covering the aspects of cloud technology.
The MITRE ATT&CK® knowledge base is explored deeper in the offensive and defensive pieces of this program. It contains adversary tactics and techniques that are utilized as the foundational development of specific threat models and methodologies.
Who Is this Program for?
Mid-level and Senior-level career professionals who have established their careers in information technology and are looking to improve their organization's preparedness and response against cyberattacks and grow their career as leaders in cybersecurity strategies will benefit most from this program.
Additionally, graduates and early career professionals with or without prior experience in the IT field who want to specialize in cybersecurity from a globally recognized school and accelerate their career in a high-growth field with high-demand job opportunities will benefit from this program.
Program Modules
Program Pillars
Pillar 1: Introduction to Cybersecurity
The first three months of this program serve as an introduction to cybersecurity with a focus on fundamental concepts and IAM (identity and access management).
Pillar 2: Defensive Cybersecurity
The second set of three months focus on defensive cybersecurity. Take a deeper dive into concepts that include cryptography, SOC (security operations center), IR (incident response), secure systems and network administration, and cloud security.
Pillar 3: Offensive Cybersecurity
The next set of months address the importance of offensive cybersecurity through topics such as penetration testing, social engineering, artificial intelligence, privacy, regulation and data governance, and OT (Operational Technology) and IoT (Internet of Things) risk.
Program Faculty
Executive Director of Cybersecurity at MIT Sloan (CAMS): The Interdisciplinary Consortium for Improving Critical Infrastructure Cybersecurity at the MIT Sloan School of Management
Dr. Pearlson is the executive director of Cybersecurity at MIT Sloan: The Interdisciplinary Consortium for Improving Critical Infrastructure Cybersecurity (IC)3. Pearlson has ...

Professor of Electrical Engineering and Computer Science, and a member of the Computer Science and Artificial Intelligence Laboratory at MIT
Dr. Zeldovich is a professor of electrical engineering and computer science at MIT and a member of the Computer Science and Artificial Intelligence Laboratory. He received his...

3Com Founders Principal Research Scientist, Founding Director, MIT Internet Policy Research Initiative, MIT Computer Science and Artificial Intelligence Lab
Daniel Weitzner is the founding director of the MIT Internet Policy Research Initiative and principal research scientist at CSAIL. In addition, he teaches internet public poli...

John Norris Maguire Professor of Information Technologies, Emeritus, Sloan School of Management, Professor of Engineering Systems, School of Engineering and Founding Director, research consortium Cybersecurity at MIT Sloan (CAMS)
Dr. Madnick is the John Norris Maguire Professor of Information Technologies, Emeritus at the MIT Sloan School of Management and the founding director of Cybersecurity at MIT ...

Ford Professor of Urban and Environmental Planning, MIT Vice Chair and Co-founder, Program on Negotiation at Harvard Law School
Prof. Susskind's research interests focus on the theory and practice of negotiation and dispute resolution, the practice of public engagement in local decision-making, cyberse...

Principal Research Scientist and Leader of ALFA Group at MIT-CSAIL
Dr. O'Reilly's research group, AnyScale Learning for All, develops new, data-driven analyses of online coding courses, deep learning techniques for program representations, ad...

Senior Security Consultant, Security Certification Educator, Lecturer at MIT Sloan School of Management
Securing information systems is Barbara's purpose and educating security professionals is her passion.
Barbara Johnson is a Senior Security, Audit and Compliance Management C...

Information Security Officer and Director of Research Computing, MIT Sloan School of Management
Rajiv Shridhar is the Information Security Officer and Director of Research Computing at MIT Sloan School of Management. He leads the team that enables the research of MIT Slo...
Principal Research Scientist at the Massachusetts Institute of Technology (MIT) Computer Science and Artificial Intelligence Laboratory (MIT CSAIL), Cambridge, Massachusetts
Howard Shrobe is a Principal Research Scientist at the Massachusetts Institute of Technology (MIT) Computer Science and Artificial Intelligence Laboratory (MIT CSAIL), Cambrid...
Program Leaders

Next-Generation Cybersecurity Leader - United Airlines, PwC, CNBC / NBCUniversal, 7Eleven, US Presidential Election Security (NDIT), AIG Founder of Israel Technologies Inc. Sr. Consultant - PaloAlto Networks
Golam Azam commands 15 plus years of core experienced versatile Cybersecurity Leadership, Teacher, Architect, Writer & Mentor with Executive MBA and outstanding Computer Engin...

Chief Executive Officer - VCNS Global
Ravish is a seasoned IT professional with over two decades of experience in enabling technology for businesses. His career spans roles with leading brands such as Hyatt, Obero...
Note: The availability of program leaders may vary across cohorts. The above profile serves as a representative persona of the program leaders.
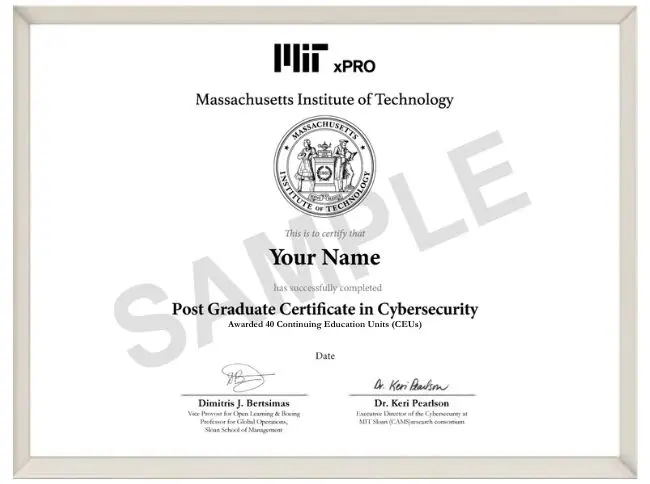
Program Certificate
Get recognized! Upon successful completion of this program, MIT xPRO grants a certificate of completion to participants and 40 Continuing Education Units (CEUs). This program is graded as a pass or fail; participants must receive 75% to pass and obtain the certificate of completion.
After successful completion of the program, your verified digital certificate will be emailed to you, at no additional cost, with the name you used when registering for the program.
Note: All certificate images are for illustrative purposes only and may be subject to change at the discretion of MIT.
Registration for this program is done through Emeritus. You can contact us at mit.xpro@emeritus.org
This program is open for enrolments for residents of India, Bangladesh, Bhutan, Myanmar, Nepal, Pakistan, Sri Lanka, Philippines, Indonesia, Thailand, Vietnam and Malaysia only.
Note:
Learning facilitator details and office hour dates and timings are from previous batches. The learning facilitators may change for upcoming batches based on availability and the office hour timings and dates may be changed based on a mutually decided schedule between Emeritus and the Learning facilitator.
*Mentioned timelines are tentative.
The Learning Experience
What is it like to learn with the learning collaborator, Emeritus?
More than 300,000 professionals globally, across 200 countries, have chosen to advance their skills with Emeritus and its educational learning partners. In fact, 90 percent of the respondents of a recent survey across all our programs said that their learning outcomes were met or exceeded. All the contents of the course would be made available to students at the commencement of the course. However, to ensure the program delivers the desired learning outcomes, the students may appoint Emeritus to manage the delivery of the program in a cohort-based manner during the course period the cost of which is already included in the overall Course fee of the course.
A dedicated program support team is available 7 days a week to answer questions about the learning platform, technical issues, or anything else that may affect your learning experience.
FAQs
Early Registrations Are Encouraged. Seats Fill Up Quickly!
Flexible payment options available.
Starts On